Digital Forensics: Investigating the 2020JimmyWilson.E01 Disk Image
A detailed walkthrough on DFIR on 2020JimmyWilson based on a coursework assignment. This documents my full investigation process using tools like Autopsy, Sleuthkit, and custom scripts
1. What is the destination time zone offset in from UTC for the following email received by Jimmy Wilson “447018D5-00000006.eml”
An offset means difference in time so the question ask for the difference in by from UTC for the email received by Jimmy Wilson The receved header for 447018D5-00000006.em is Message:Raw-Header:X-Received: by 10.236.89.11 with SMTP id b11mr22181676yhf.16.1392573313406; Sun, 16 Feb 2014 09:55:13 -0800 (PST) 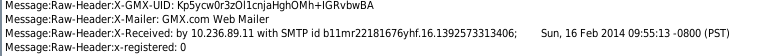
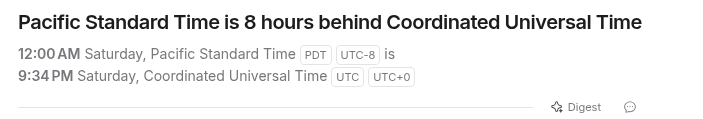
9:55 PST converted to UTC 0 is 5:55 PM UTC -8 also -0800 in the message header means UTC -8 link to converter used
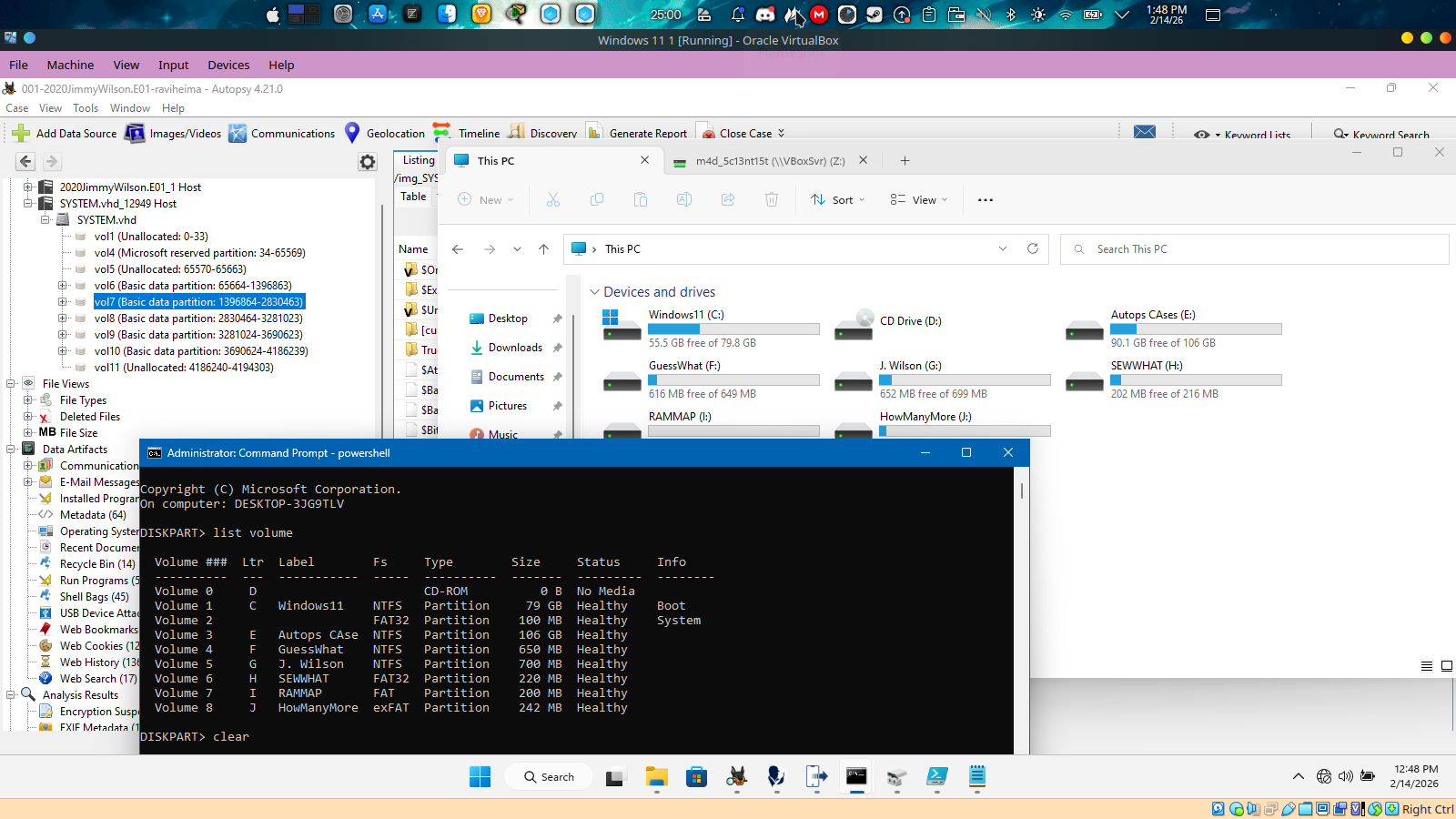
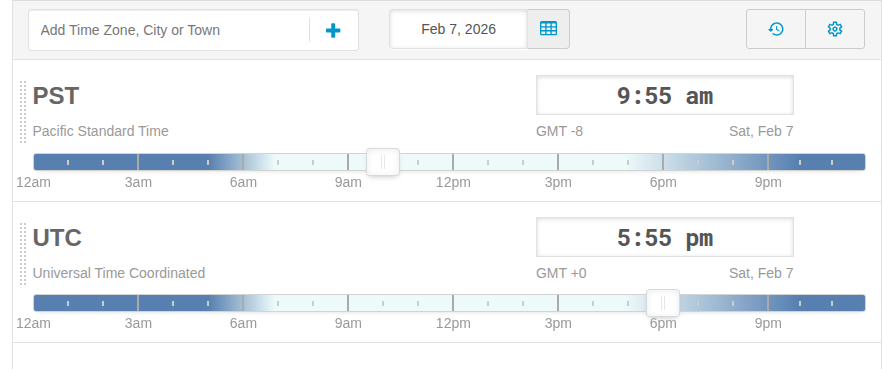
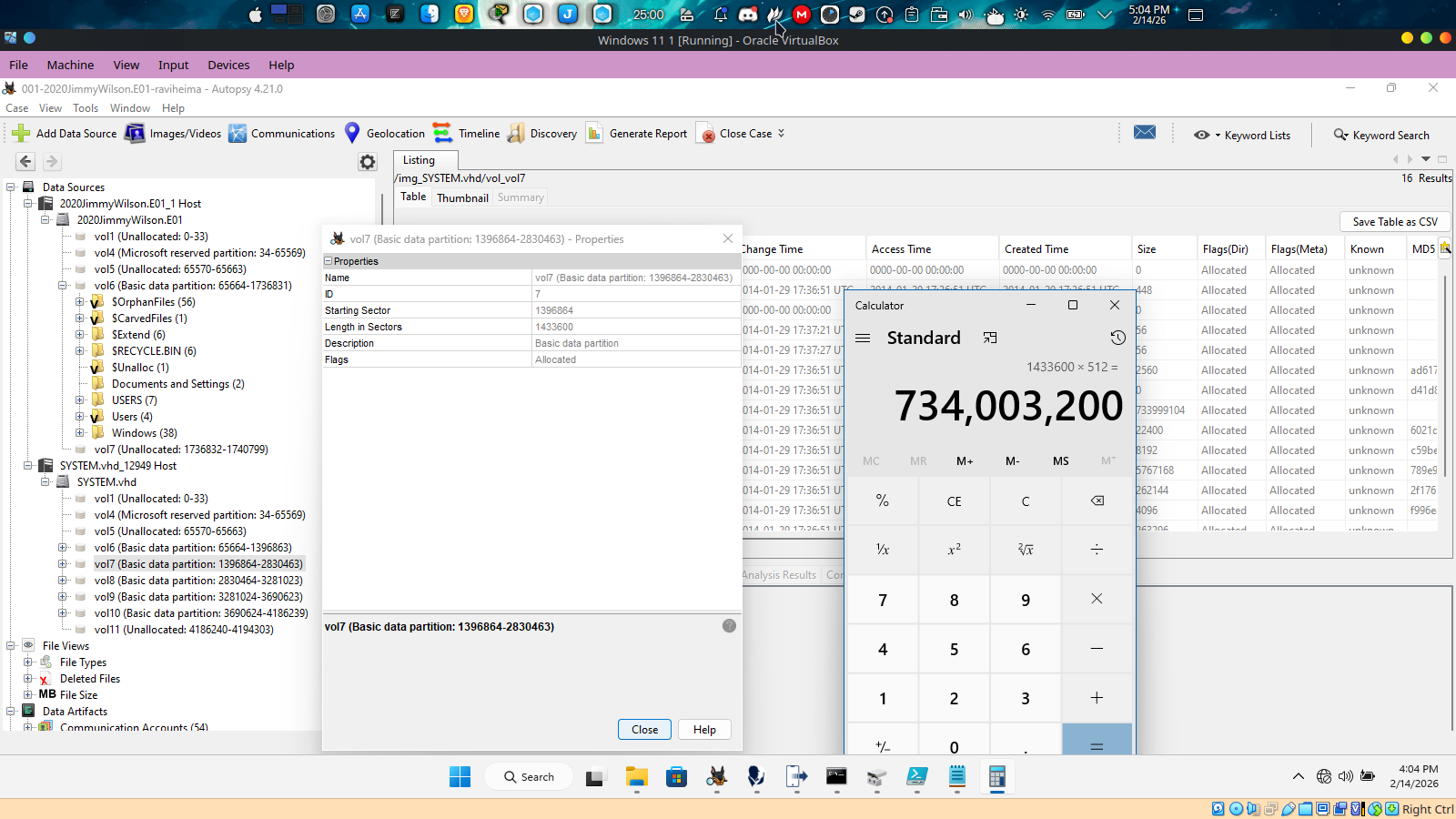
2. What is the total capacity in bytes (decimal) of the partition labeled “J. Wilson” found in
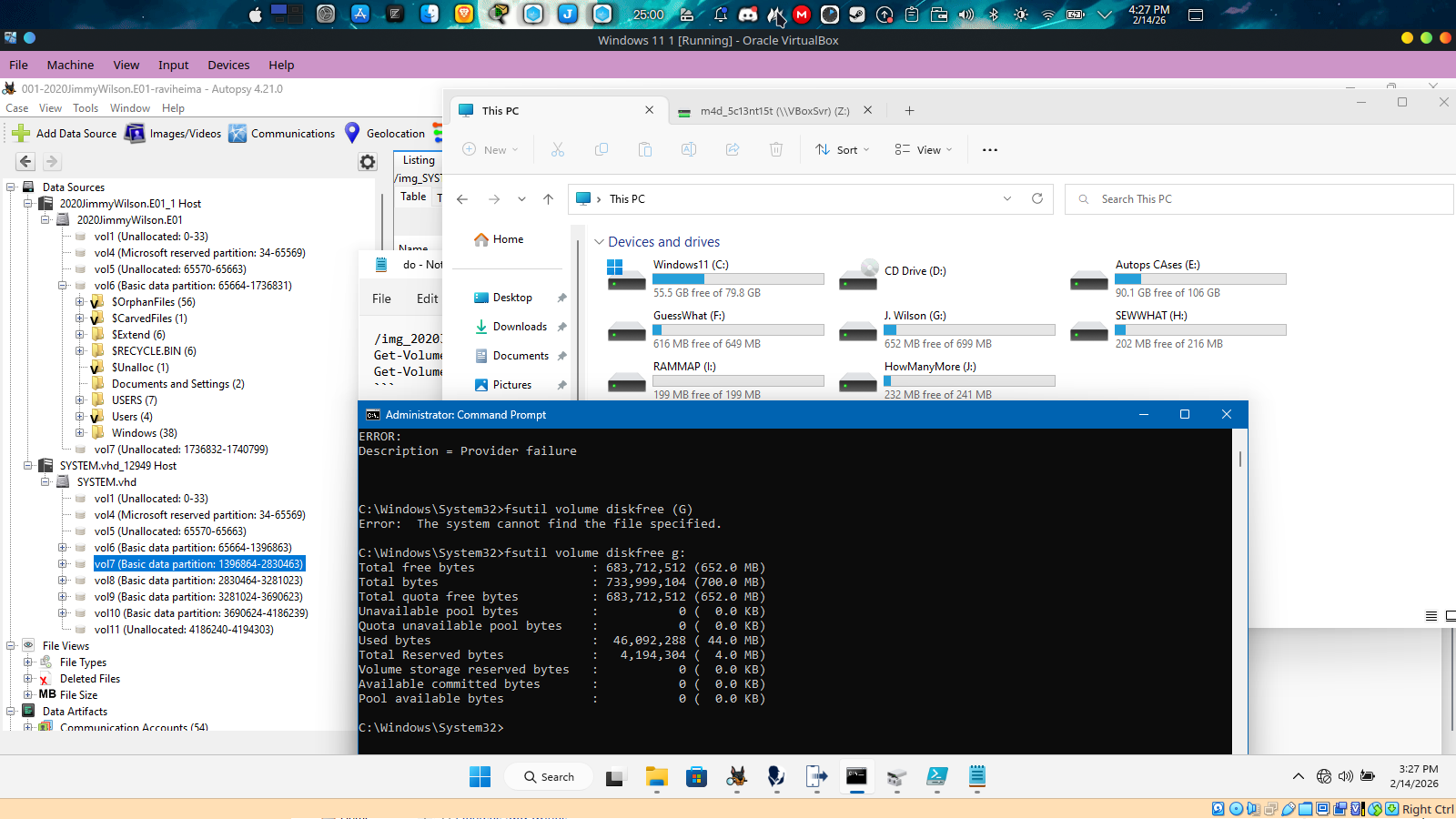
system.vhd located at /img_2020JimmyWilson.E01/vol_vol6/Windows/System32/config/SYSTEM.vhd then i doubled click on the system.vhd file to mount it after mounting it i found a couple of partitions with their label including the one labeled “J.wilson” using windows cmd diskpart list of commands i used
1
2
3
4
5
6
7
8
9
diskpart
list disk
select disk 2
list volume
#volume 5 shows label J. Wilson with Ltr G
exit
#use fsutil to get disk details
fsutil volume diskfree g:
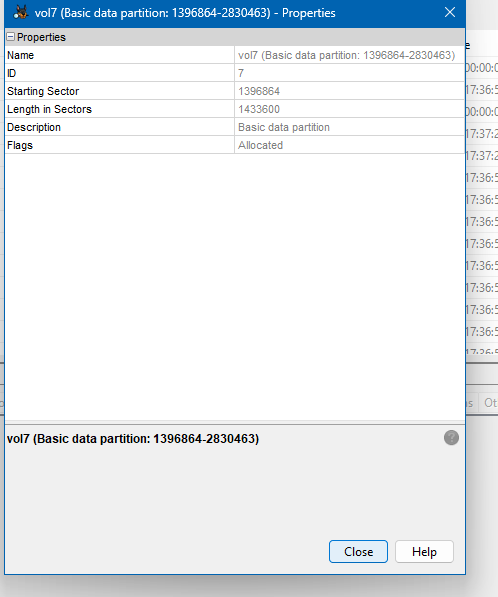
i opened the J.wilson volume and it contains the truecrypt directory and in autopsy the volume containing truecrypt is vol7, so this is a solid evidence that vol7 is the vol with the label and to get the bytes in size we use the vol lenght in sectors which is 1433600 multiply it by 512 the product is 734,003,200
3. What was the date and time the following email received by Jimmy Wilson "447018D5-00000006.eml" was originally sent?
According to the header 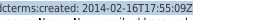
dcterms:created: 2014-02-16T17:55:09Z which means February - 16 - 2014- 17:55:09 where Z is a suffix for the aviation code for UTC 0 so 17:55 - 5 = 12:55 UTC -05:00 so the answer is c. Sun, 16 February 2014 12:55:09 -05:00
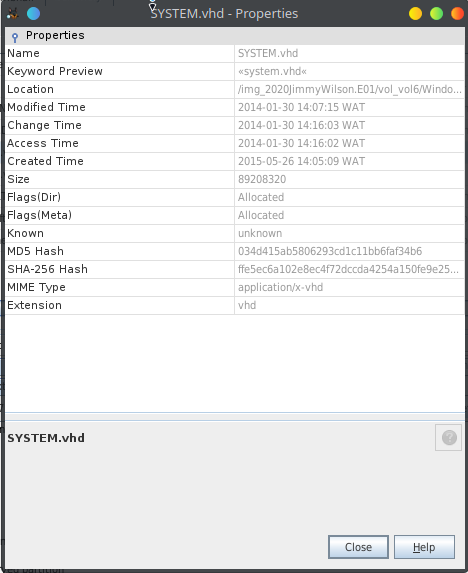
4. The physical disk contains a Virtual Hard Drive which is greater than 10MB in size, the full name of the file is: system.vhd:
The system.vhd virtual hard disk file location path in the physical drive is Windows/System32/config/SYSTEM.vhd which is suspicious as vhd files don’t belong to system32\config directory this indicates hiding of data
The disk physical file size is 89208320bytes which is 85.08mb (89208320bytes / 1,048,576bytes(mib) =85.07 MB) > 10Mb
and The Virtual Disk size is 2147483648 which is 2Gb (2147483648/1,048,576(mib) = 2048MB) > 10 mb both the physical file size of the system.vhd virtual disk and the logical virtual size are greater than 10mb 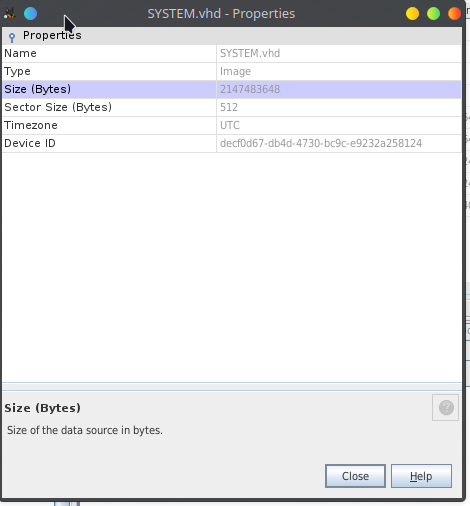
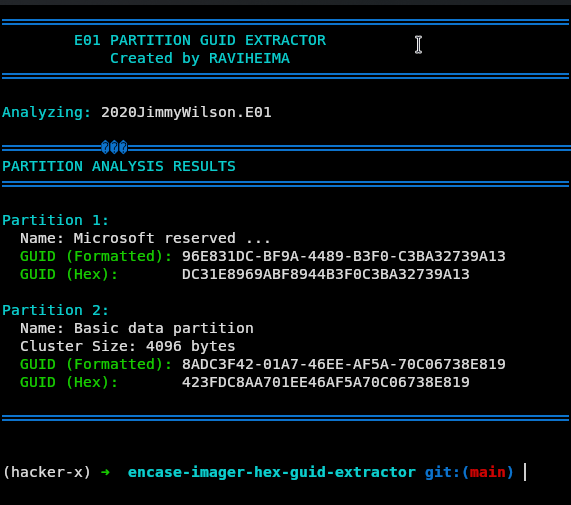
4. The disk GUID (in hex) of the physical disk is: 6FAE8D386C441743AE3298C4BDE04830 Select one:
using a custom script to get the guid 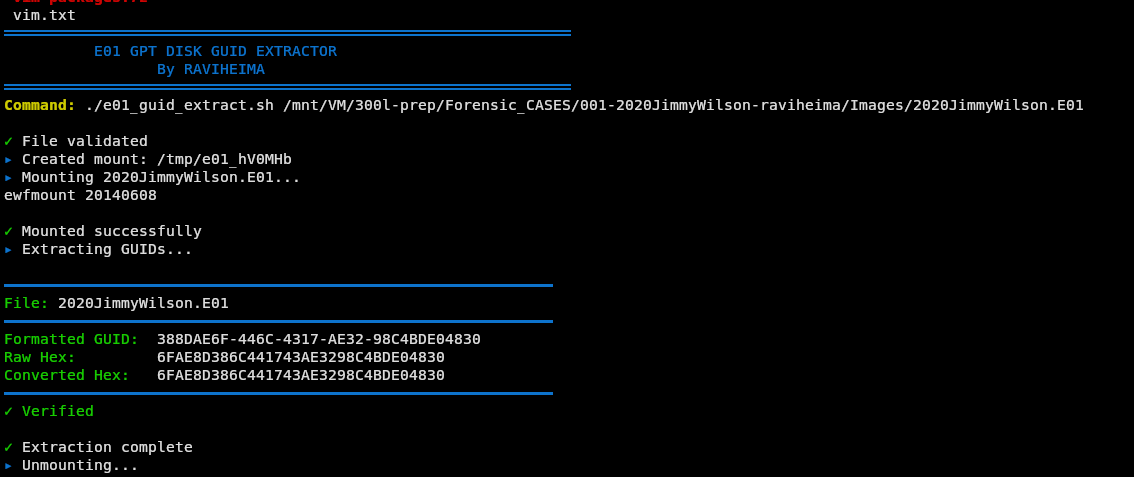
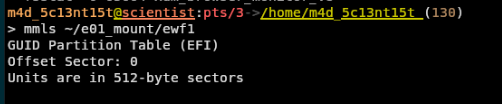
5. What is the cluster size in bytes within the second partition of the physical disk? Select one:
using a command line tool called efwmount(Expert Witness Format Forensic Images)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
# Create mount point in home directory
mkdir -p ~/e01_mount
# Mount the E01 file using ewfmount
ewfmount /mnt/VM/300l-prep/Forensic_CASES/001-2020JimmyWilson-raviheima/Images/2020JimmyWilson.E01 ~/e01_mount
# Display partition table using mmls (Memory Management Layer System)
mmls ~/e01_mount/ewf1
# Get cluster size for partition 2 (offset 65664)
fsstat -o 65664 ~/e01_mount/ewf1 | grep -i "cluster"
# Unmount the E01 image
fusermount -u ~/e01_mount
# Optional: Remove mount point directory
rmdir ~/e01_mount
First and second partition 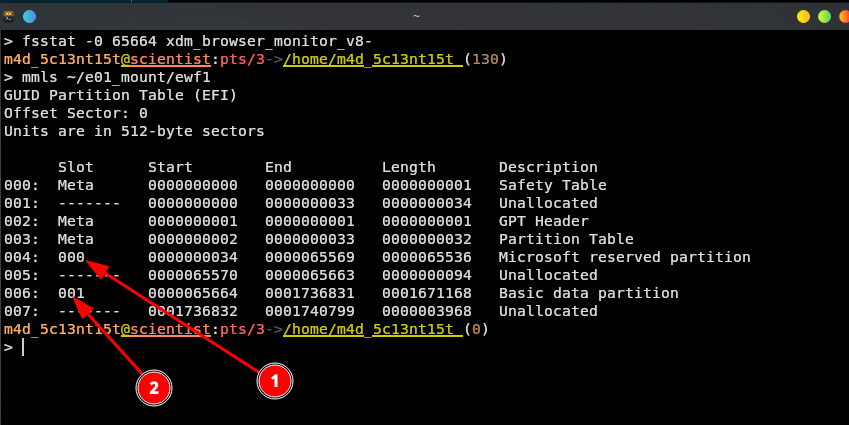
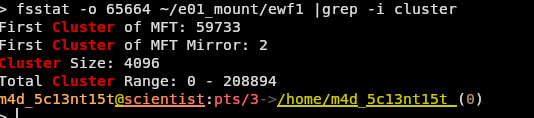
4096
6. On February 20, 2014 @ 17:02:35 UTC -00:00, what was the system up time in
seconds is: 9,634 To answer this question we have to first extract the windows event log file located at /Windows/System32/winevt/Logs/System.evtx You need a windows VM or Machine to complete this tasks after extracting file to your Windows host machine, then open the extracted file with windows event viewer 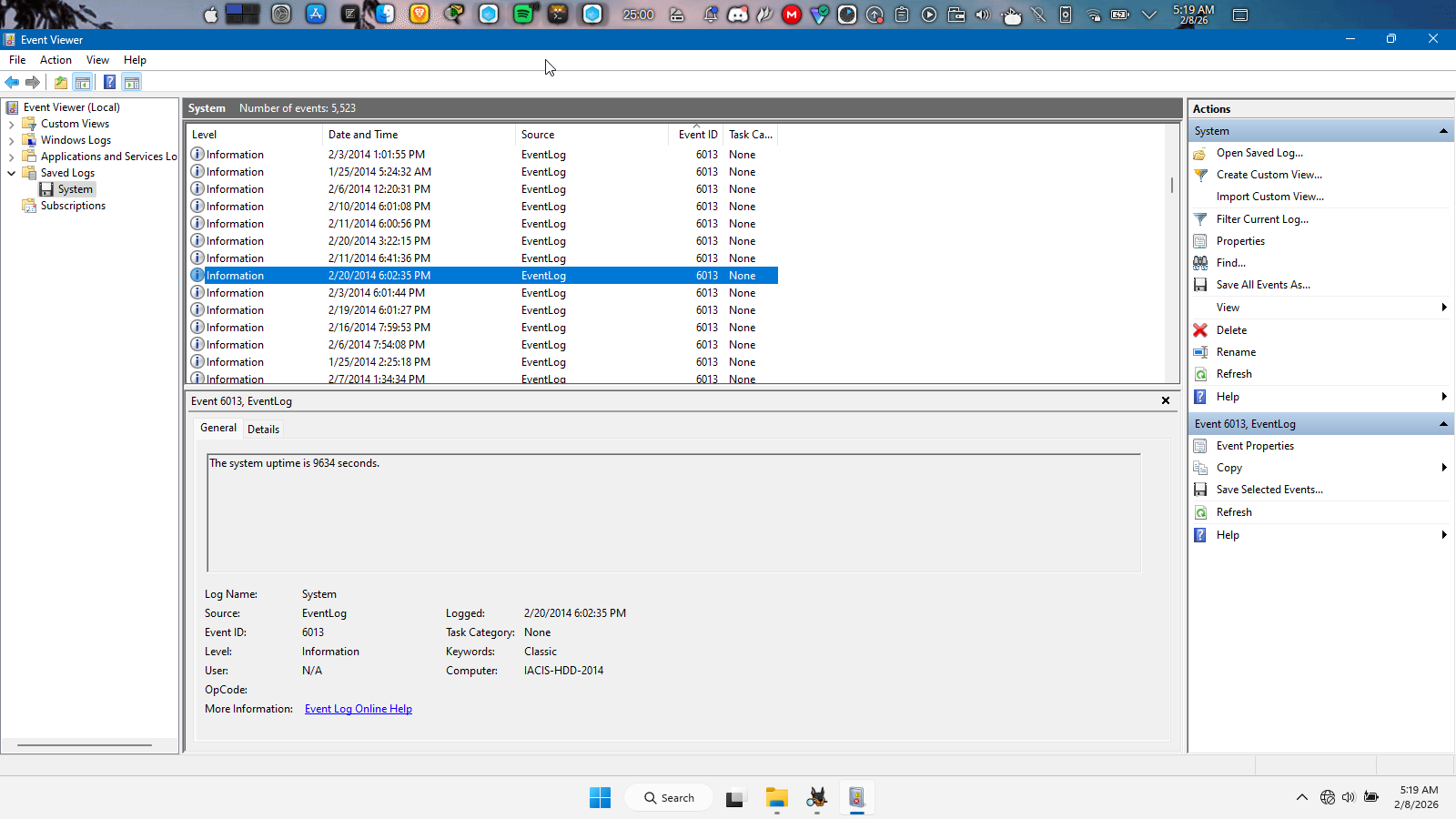
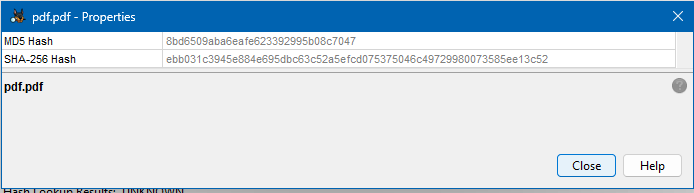
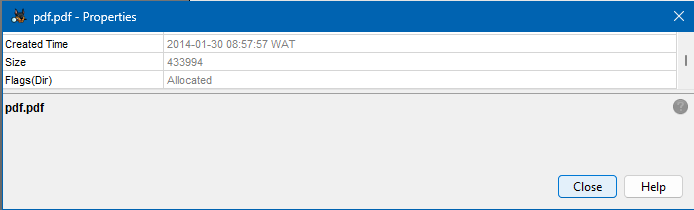
7. The MD5 hash value of the pdf.pdf file is: C1F95108A34228535A9262085E784D7C3E27FC68
The pdf.pdf file is located in the system.vhd Virtual Hard Disk Vol8 partition full path is SYSTEM.vhd/vol_vol8/pdf.pdf
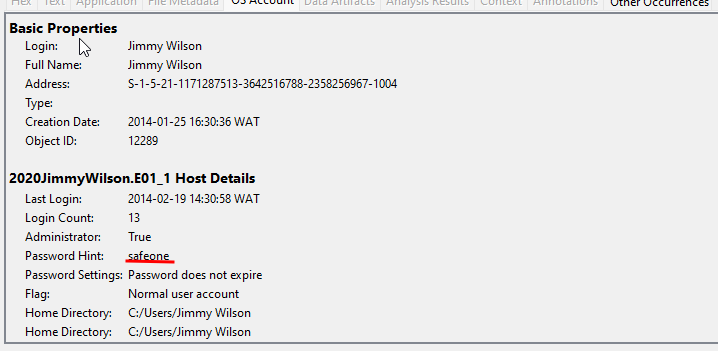
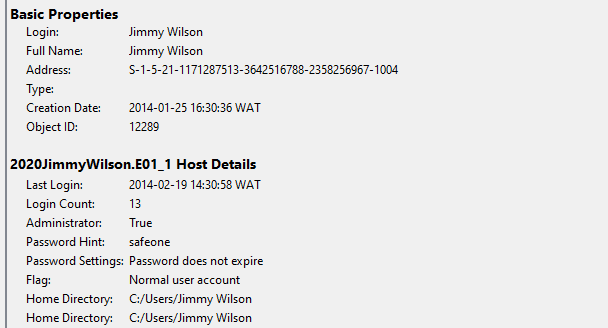
8. The user account Jimmy Wilson has his logon password enabled and the password hint is safeone.
9. What is the partitioning format (Schema) of the physical disk?
10. The final destination IP Address for the following email received by Jimmy Wilson “447018D5-00000006.eml” is: 10.221.48.196
1
2
3
4
5
6
7
8
9
10
11
12
13
14
uthor: Robert Ripoff <robert.ripoff@gmx.com>
Content-Type: message/rfc822
Creation-Date: 2014-02-16T17:55:09Z
Message-From: Robert Ripoff <robert.ripoff@gmx.com>
Message-To: wilsonjimmy807@gmail.com
Message:From-Email: robert.ripoff@gmx.com
Message:From-Name: Robert Ripoff
Message:Raw-Header:Authentication-Results: mx.google.com; spf=pass (google.com: domain of robert.ripoff@gmx.com designates 74.208.4.200 as permitted sender) smtp.mail=robert.ripoff@gmx.com
Message:Raw-Header:Delivered-To: wilsonjimmy807@gmail.com
Message:Raw-Header:MIME-Version: 1.0
Message:Raw-Header:Message-ID: <20140216175509.190490@gmx.com>
Message:Raw-Header:Received: by 10.221.48.196 with SMTP id ux4csp77384vcb; Sun, 16 Feb 2014 09:55:13 -0800 (PST)
Message:Raw-Header:Received-SPF: pass (google.com: domain of robert.ripoff@gmx.com designates 74.208.4.200 as permitted sender) client-ip=74.208.4.200;
Message:Raw-Header:Return-Path: <robert.ripoff@gmx.com>
1
The answer is true
11. The 2nd partitions unique GUID (in hex) of the physical disk is: 423FDC8AA701EE46AF5A70C06738E819
The answer is true
12. What is the logical size in bytes (decimal) of the pdf.pdf file?
13. The User account BillyBob sent the following files to the $recyclebin: New Price List.txt and New Price List Encoded.
i. The `New Price List encoded is located at
1
/img_2020JimmyWilson.E01/vol_vol6`/`$`RECYCLE.BIN/S-1-5-21 1171287513-3642516788-2358256967-1004/$R3TS6GA/New Price List Encoded.TXT
ii.The New Price list is located at
1
/img_2020JimmyWilson.E01/vol_vol6/$RECYCLE.BIN/S-1-5-21-1171287513-3642516788-2358256967-1004/$R3TS6GA/New Price List.txt
so The answer is True
14. What is the logical file size in bytes (decimal) of the PLEAS.txt file?
The pleas.txt file is located at /img_SYSTEM.vhd/vol_vol10/PLEAS.txt 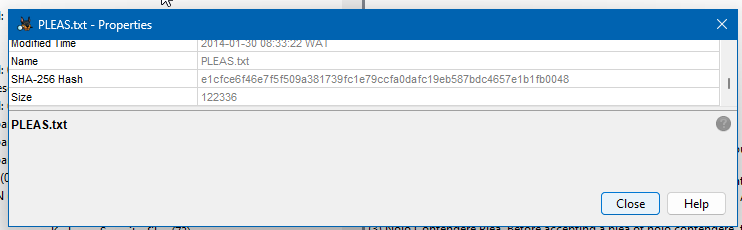
12236
15. Provide the full name of the User that has the RID number 0x3EB:
To identify the user with RID number 0x3EB: Click On Os Accounts in autopsy 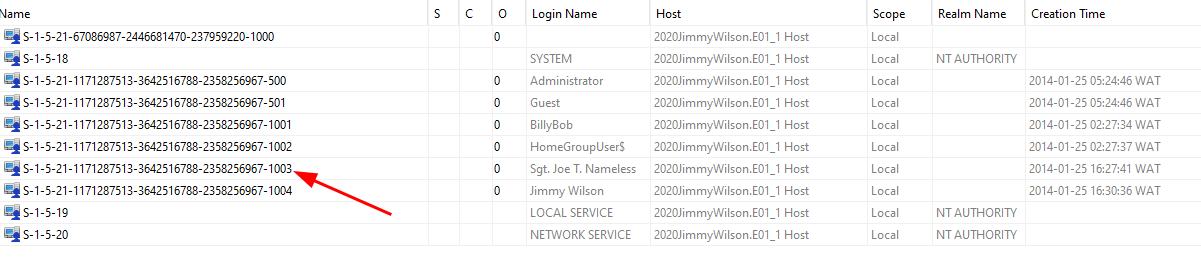
1
2
3
4
5
6
7
S-1-5-21-1171287513-3642516788-2358256967-1003
│ │ │ │ │────────────────────────────────│ │
│ │ │ ��� Domain │ RID
│ │ │ └─ NT Authority │
│ │ └─── Security Authority (5 = SECURITY_NT_AUTHORITY)
│ └───── Revision Level
└─────── "S" indicates it's a SID
And the RID is the last number after a dash 1003 converting 1003 to hex results in 0x3eb 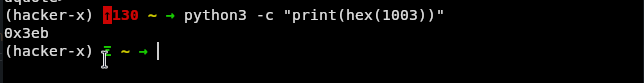
16. When was the last log-in date and time for the User “Jimmy Wilson”?
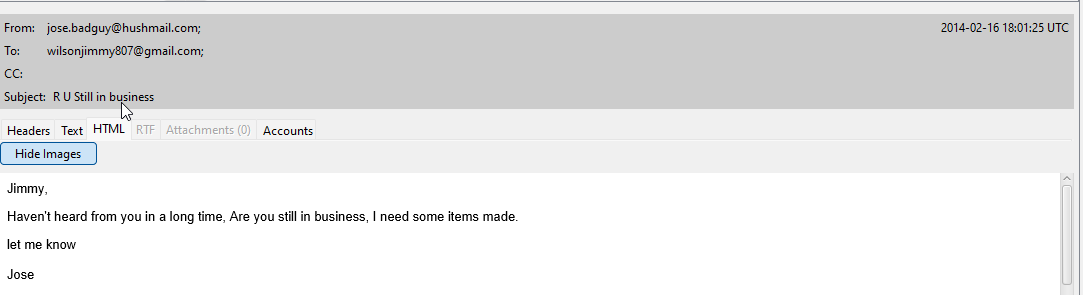
17. The following individuals: jose.Badguy@hushmail.com, robert.ripoff@gmx.com sent emails to the User Jimmy Wilson?
It’s Evident that Jimmy received emails from jose. and robert 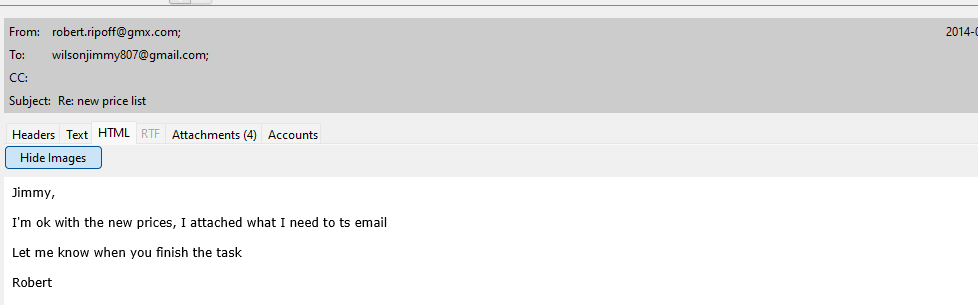
18. What program did the User Jimmy Wilson have set to run when he logged on to the
computer? To find out we’ll open to registry located at /img_2020JimmyWilson.E01/vol_vol6/USERS/Jimmy Wilson/NTUSER.DAT Then navigate to Software → Microsoft → Windows → CurrentVersion → Run → RESTART_STICKY_NOTES 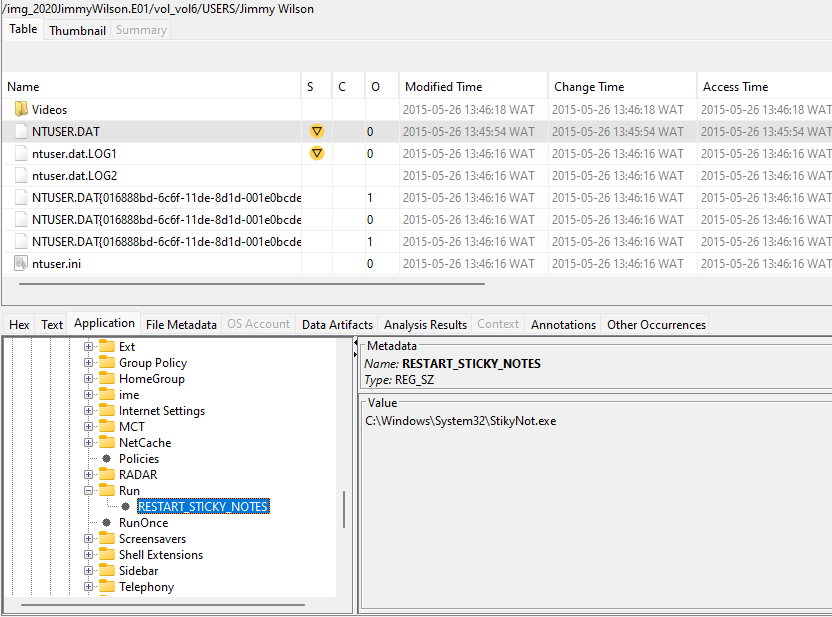
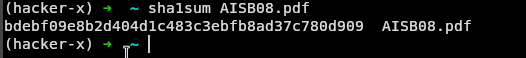
19. The SHA1 hash value for the AISB08.pdf file is: BDEBF09E8B2D404D1C483C3EBFB8AD37C780D909
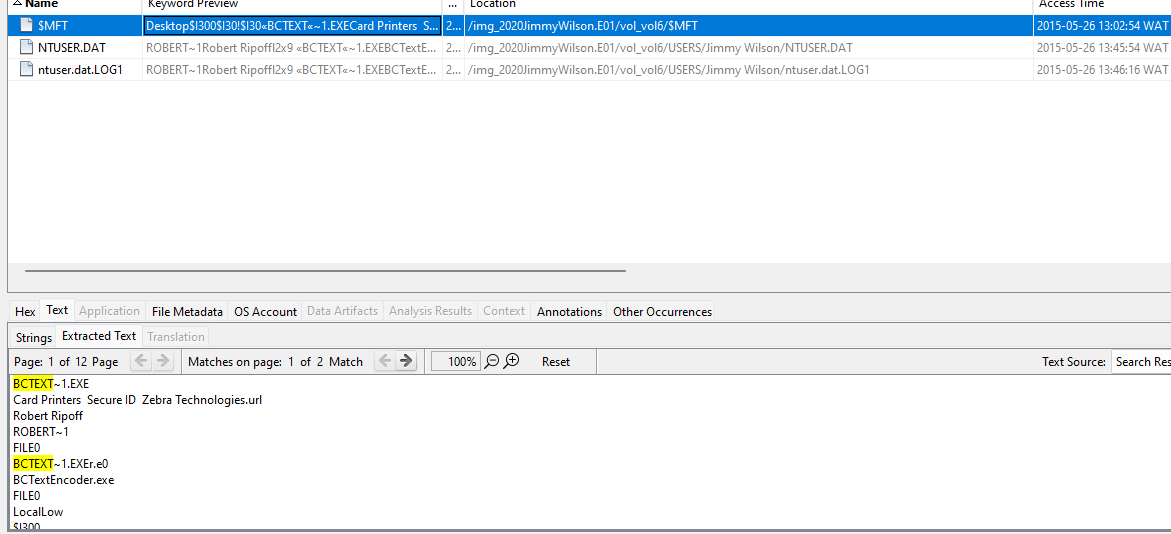
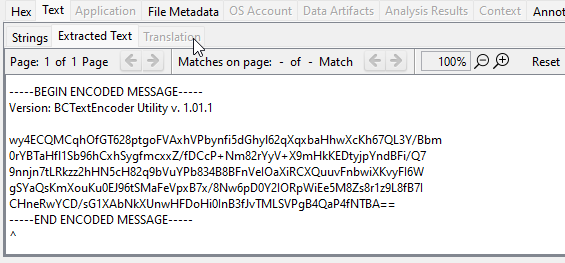
20. What encryption programs were used on this computer? The Encryption Programs used on this computer are
Bcrypt/TrueCrypt As they were the only Encryption Programs found in the system aside from bitlocker which is installed by default 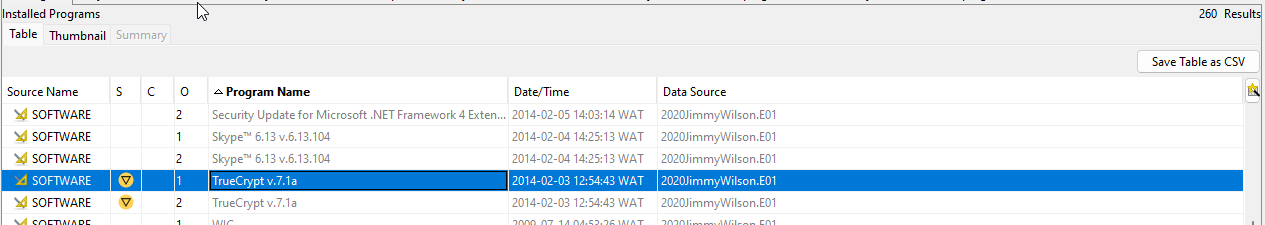
22. The SHA1 hash value for the Card Printers.htm file is: F6CF04DB3D1BA828E375BBFE988876CE06164126:
1
2
3
The `Card Printers.htm` file is located at `/img_SYSTEM.vhd/vol_vol8/Card Printers.htm`
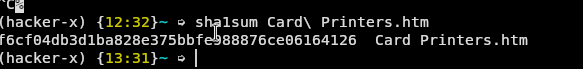
The answer is True
23. What search engine did the User “Jimmy Wilson” use to search for: how to steal identities?
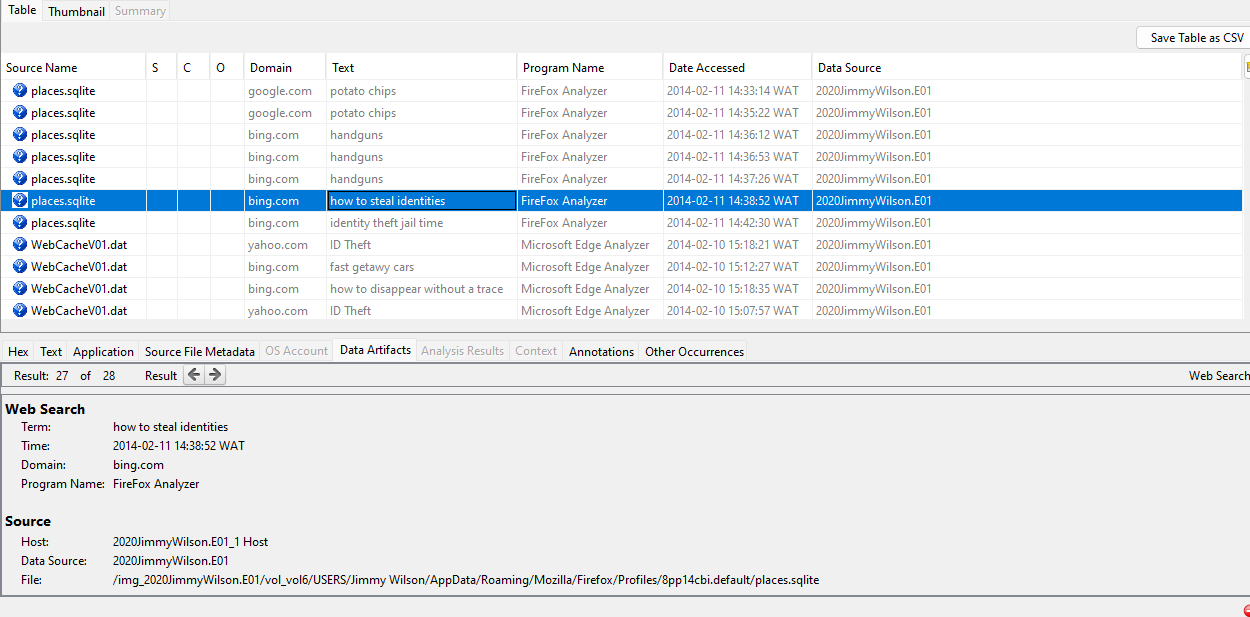
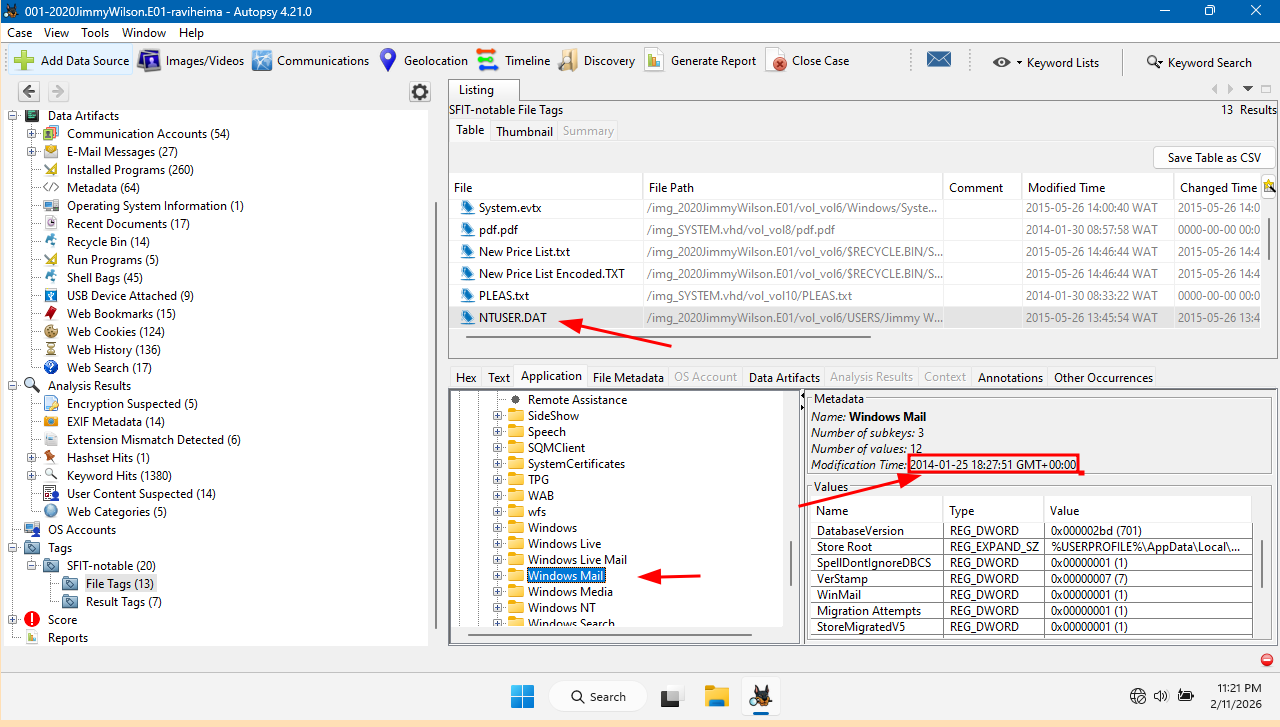
24. What is the last Date/Time the User “Jimmy Wilson” last ran the Windows Mail Application?
To find this Go to the user registry ( NTUSER.dat) located at /img_2020JimmyWilson.E01/vol_vol6/USERS/Jimmy Wilson/NTUSER.DAT Software -> Microsoft -> Windows Mail(Click on windows mail) and by your left the last modified date in the registry is the
Paths Investigated — No Results
1. UserAssist Registry Key
1
2
NTUSER.DAT → Software → Microsoft → Windows →
CurrentVersion → Explorer → UserAssist
Result: No Windows Mail entry found
2. Prefetch Folder
1
/img_2020JimmyWilson.E01/vol_vol6/Windows/Prefetch/
Result: No MSIMN.EXE prefetch file found — prefetch likely disabled
3. LNK / Recent Files
1
/vol_vol6/Users/Jimmy Wilson/AppData/Roaming/Microsoft/Windows/Recent/
Result: Directory not found
4. Jump Lists
1
/vol_vol6/Users/Jimmy Wilson/AppData/Roaming/Microsoft/Windows/Recent/AutomaticDestinations/
Result: Directory not found
Paths That Yielded Results
1. Windows Mail Registry Key (Primary)
1
2
NTUSER.DAT → Software → Microsoft → Windows Mail
Modification Time: 2014-01-25 18:27:51 GMT+00:00
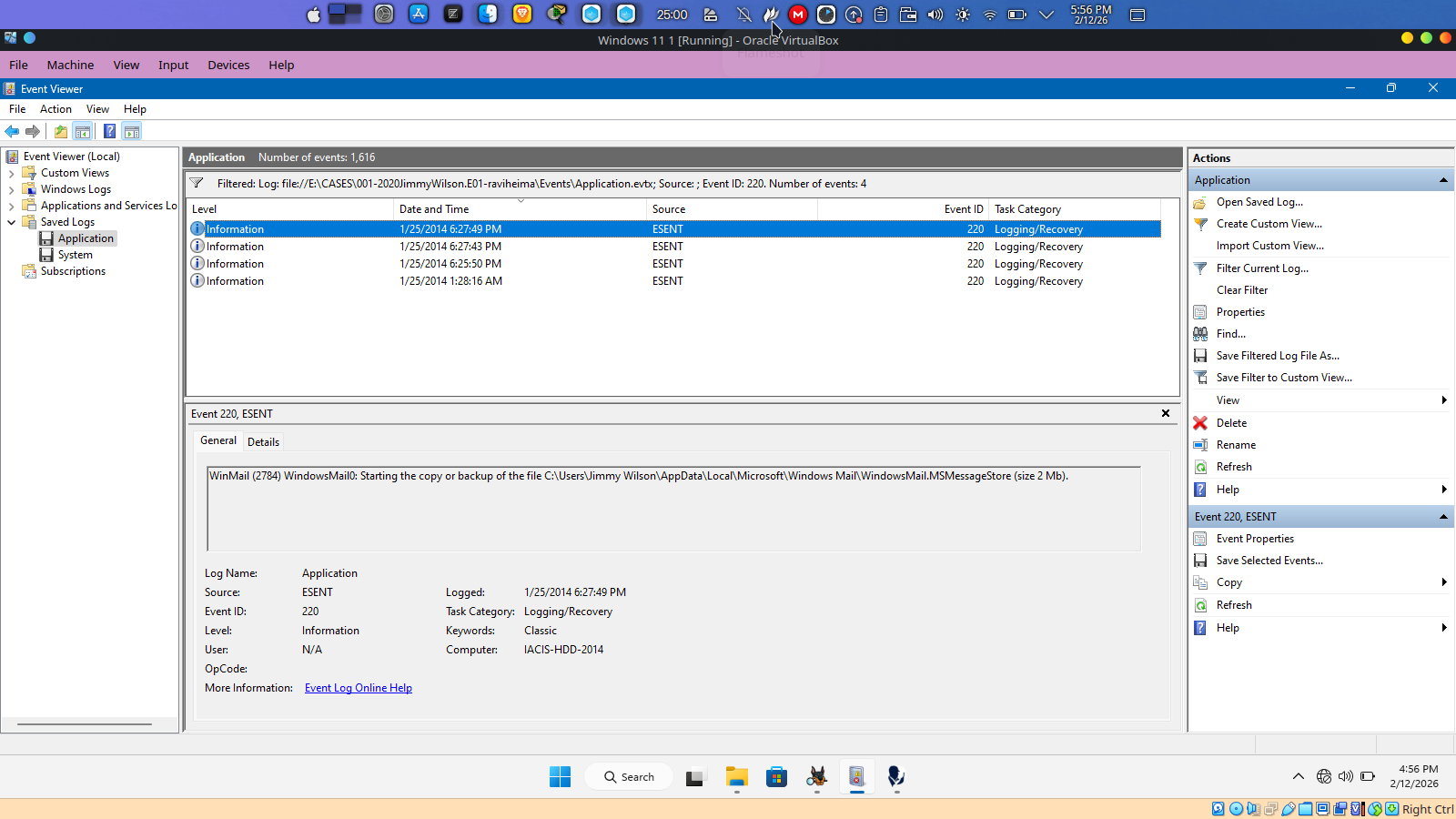
2. Application.evtx — ESENT Event ID 220 (Corroboration)
1
2
3
4
/img_2020JimmyWilson.E01/vol_vol6/Windows/System32/winevt/Logs/Application.evtx
Source: ESENT | Event ID: 220
Timestamp: 1/25/2014 10:27:49 AM PST = 18:27:49 UTC
Description: WinMail database backup operation
25. What is the SHA1 hash value of the Physical Disk?
Select one: using ewfinfo a sleuth kit util to get the hash for the physical disk
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
$ ewfinfo 2020JimmyWilson.E01 [7:28:48]
ewfinfo 20140608
Acquiry information
Case number: 1
Description: Jimmy Wilson
Examiner name: CEDONLEY
Evidence number: 2
Notes: 2018 Recertification
Acquisition date: Thu Dec 14 11:52:41 2017
System date: Thu Dec 14 11:52:41 2017
Operating system used: Win 201x
Software version used: ADI3.4.2.6
Password: N/A
EWF information
File format: FTK Imager
Sectors per chunk: 64
Compression method: deflate
Compression level: no compression
Media information
Media type: fixed disk
Is physical: yes
Bytes per sector: 512
Number of sectors: 1740800
Media size: 850 MiB (891289600 bytes)
Digest hash information
MD5: b267fb0cd94645425eee00258d3a9b58
SHA1: a1102c70a50768b588225fdcad6efa5d5d57341b
(hacker-x)
m4d_5c13nt15t@scientist /mnt/VM/300l-prep/Forensic_CASES/001-2020JimmyWilson-raviheima/Images
The answer is a. a1102c70a50768b588225fdcad6efa5d5d57341b
github script used for number 4 and 11